The Digital Battlefield: Ethical vs. Malicious Hackers
Introduction
Do you know that in 2011, Citibank (Citigroup) suffered a cyber attack that resulted in the theft of almost $2.7 million?
The actors just took advantage of a simple data breach on their website. They had been exploiting it for months before it was detected. The bank suffered a lot from that since over 360K accounts have been affected, and it was quite a challenge to get rid of it.
Summary
Birth of Information Security
In the last two decades, computer science has grown drastically; a lot has been discovered and a lot has been improved. Nowadays, computers and technologies have nothing to do with the ones that existed in the beginning, at least in their forms and functionalities. That's what raised a new treasure, a treasure that wasn't easily reachable before. A lot would have been different with it, that's Information.
The importance of information has become so high that it could save human lives! It's also very important in our daily lives, and we find it in many forms. In this article, we are going to talk about digital information, in other words information stored on computers, and we are going to refer to that as data.
Data is everywhere, in schools, hospitals, banks, governments, militaries, super markets, etc. So basically, everyone in the world has data. Its importance differs from one person to another and from one usage to another; it might be very critical sometimes.
Unfortunately, since nothing is perfect in this world, access to this information could be compromised. That's mostly due to the human factor in many forms. It can be either an error, a miss, or sometimes simply negligence. This can lead to leave security holes in a digital system, we refer to these hole as vulnerabilities.
And there are many people with malicious intentions trying to take advantage of these vulnerabilities and target them for their own sake. They are called Hackers.
Hackers are seen as criminals, and that's far from being wrong. The consequences of their acts might be disastrous, including money loss and the ruin of many people's lives, but sometimes there are minor damages that can't be negligible. We are going to take a look at some of these consequences later on.
Their existence has made it inevitable to take care about Information Security by having people fighting against them (hackers).
They are called Ethical Hackers, their job is to basically prevent or minimize hackers' attacks (also known as cyber attacks). They are people who work to make the digital world a safer place.
Cyber Attacks
So, cyber attacks, as have been introduced before, are acts of hackers. Hackers attack systems in order to steal, perform unauthorized changes, or even destroy data for many malicious purposes.
Most of these attacks could be categorized into one of these three categories.
Attacks against systems
In this case, the vulnerabilities are generally caused by a technical mistake in the system. Hackers use their knowledge of the system and how it works to find an untended way of using it in their favor, and they can get unauthorized access to a resource or even the system as a whole.
We speak generally about:
-
Zero Day exploits (recently discovered vulnerabilities that haven't been patched, which means that they are still present in the latest version of the system).
-
CVEs (codes of vulnerability exploits) are proofs of concepts that are relevant against outdated systems.
-
Man-in-the middle attacks, Denial Of Service (DOS), Distributed Denial Of Service (DDOS) etc.
Attacks against people
It's widely known that the most vulnerable point in a digital system is humans. It's the most unpredictable actor within it. Many cyber attacks have actually been performed against people working in companies, exposing critical data or performing disastrous actions in many systems.
Here is a quote I want to expose
There is no patch for human stupidity
Which means that nothing can be done when a hacker succeeds in hacking people themselves! Here we talk more about social engineering, which aims to hack the mentality of a person by using many techniques like phishing.
Attacks against systems through people
In this case, the aim of the attack is generally to destroy data or malfunction a system. This is done by making people use malicious computer programs called malware.
These are programs that either destroy data, completely change its form, making it unusable, or even leak it, which leads to severe consequences. And that's the job of
-
viruses: programs that spread very quickly on a system or in a network
-
ransomware: malware that encrypts data via a strong algorithm and asks for a ransom in order to get it back.
-
Trojans, worms etc.
-
On the other hand, malware can stay idle and only steal data, as spyware does.
And as you see, these are only achieved by human errors that include them in the system in some way or another.
Some Critical Cyber Catastrophes
In the last decade, the world has known numerous cyberattacks that have had severe consequences.
This made organizations care more about their system security.
Here are some of the most known ones:
- Sony Pictures Hack (2014)
The cyberattack on Sony Pictures Entertainment in 2014, which was attributed to North Korea, led to the exposure of confidential data, including unreleased films and sensitive employee information. The perpetrators, operating under the pseudonym "Guardians of Peace," demanded that Sony halt the release of the movie "The Interview," which featured a fictional plot involving the assassination of North Korea's leader.
- WannaCry Ransomware (2017)
WannaCry, a worldwide ransomware assault, specifically sought out computers utilizing outdated Windows versions. This malicious program propagated swiftly, impacting both organizations and individuals across the globe. It exploited a security vulnerability purloined from the NSA to encrypt victims' files, prompting them to pay a ransom for data decryption. Before substantial damage occurred, a security researcher fortuitously identified a mechanism to halt the attack.
- SolarWinds Cyberattack (2020)
The SolarWinds cyberattack was an intricately planned supply chain breach that targeted SolarWinds, a prominent IT management firm. The assailants compromised SolarWinds' software updates, providing them with access to the systems of various entities, including government agencies and prominent corporations. The attack was linked to a Russian Advanced Persistent Threat (APT) group.
- Log4j (2021)
Log4j, a well-established Java utility with a two-decade history, encountered a pivotal moment in December 2021 with the discovery of a critical vulnerability named Log4Shell. This flaw permitted unauthenticated and unskilled malicious actors to take control of applications, leading to expensive security breaches.
- Twitter (5.4 Million User Accounts Stolen From a Social Engineering Attack 2022)
On August 5, 2022, Twitter made a startling announcement, revealing that a hacker, operating under the pseudonym "devil," had exploited a zero-day vulnerability. This breach allowed them to connect personal identification details like phone numbers and email addresses with user accounts on the social media platform.
Seizing the opportunity presented by this vulnerability, the hacker subsequently released a vast dataset on online forums, pricing it at $30,000. The bug's existence had become publicly known in June 2021, impacting more than 5 million users.
In response to this incident, Twitter acted swiftly, directly reaching out to affected account owners and offering guidance. They urged users to implement two-factor authentication as an essential safeguard against unauthorized access to their accounts.
Ethical Hackers
As stated before, the rise of hackers in the tech field made organizations think about solutions to increase their system security.
Thus, they had to find positions or jobs that would pay for reviewing these systems and detecting vulnerabilities in order to patch or fix them. The people who are taking these positions are actually the ones we call ethical hackers.
Ethical hacking is divided into two main categories
-
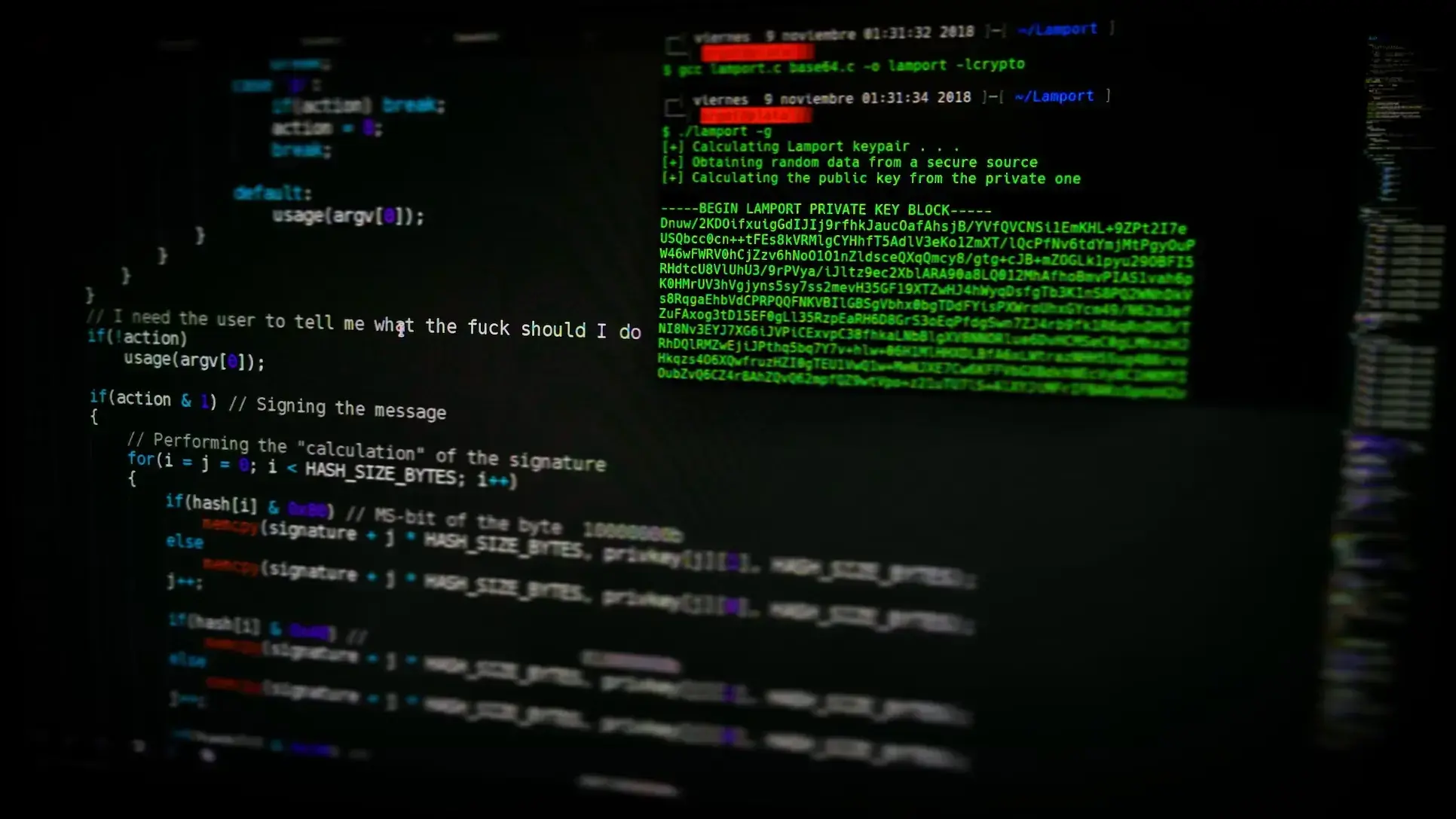
Offensive Security: Also known as penetration testing or ethical hacking, is the practice of simulating cyberattacks on an organization's systems to identify vulnerabilities and weaknesses. The main goal of offensive security is to proactively discover and address security issues before malicious actors can exploit them.
-
Defensive Security: It focuses on protecting an organization's systems, data, and network infrastructure from potential threats. Its primary goal is to prevent unauthorized access, data breaches, and other security incidents.
Ethical hacking takes generally different approaches or teams when securing a system; some of these are:
-
Red teaming: is a structured and systematic approach to testing and evaluating the security of an organization's systems, processes, and defenses. It involves simulating cyberattacks and other threats to assess an organization's security posture, vulnerabilities, and overall resilience. The primary goal of red teaming is to provide an unbiased and realistic assessment of an organization's security capabilities and identify weaknesses that might not be apparent through traditional security testing methods.
-
Blue Teaming: Blue Teams are responsible for protecting an organization's digital assets, systems, and data from cyber threats, while also working to detect and respond to security incidents. In contrast to red teams, which simulate attacks and adversarial activities, blue teams are primarily concerned with maintaining and improving the organization's security posture
-
Purple teaming: is a collaborative and integrated approach to cybersecurity that combines the efforts of both red teams and blue teams within an organization. The goal of purple teaming is to improve an organization's overall security posture by facilitating communication, knowledge sharing, and joint testing between these two teams
There are other types of teams that are more specialized, as the image below shows
Regarding the importance of their role in the information world, there are multiple organizations and enterprises that are specialized in providing services in the infosec field, like penetration testing and application review.
Not only organizations but freelancers in this field have seen an interesting rise with the appearance of Bug Bounty Hunting programs (programs launched by companies that reward individuals for reporting vulnerabilities they find on their systems).
Conclusion
As a conclusion, we must state that the war between ethical and unethical hackers is not something that could be ended as long as digital information remains a critical resource.
Everybody should be aware of information security practices that don't require technical knowledge at all. And thinking about having a career in cyber security is an interesting choice since ethical hackers are highly demanded out there, and there are many resources to start learning right away! So, to end this article, we have a question for you. Have you ever been affected by a cyberattack like phishing, or have you already been affected by ransomware or a virus? Let us know about it!
Become a certified cybersecurity expert. Code Labs Academy's Cybersecurity Bootcamp prepares you with the certifications and practical skills you need to launch a successful career.